Analysis reveals that detecting and eradicating smartphone spyware and adware functions is difficult.
A staff of laptop scientists from New York and San Diego has discovered that smartphone spyware and adware functions, which allow people to observe one another, aren’t solely troublesome to establish and detect however are additionally vulnerable to inadvertently exposing the delicate private knowledge they collect.
Though marketed as instruments for supervising minors and staff utilizing company-owned units, spyware and adware apps are sometimes exploited by abusers to secretly monitor a partner or accomplice. These functions demand minimal technical data from the perpetrators, present complete set up steerage, and merely require non permanent entry to the goal’s machine. As soon as put in, they discreetly doc the sufferer’s machine utilization—together with textual content messages, emails, photos, and cellphone calls—enabling abusers to remotely entry this info by way of an internet portal.
Spy ware has turn out to be an more and more major problem. In a single current examine from Norton Labs, the variety of units with spyware and adware apps in the USA elevated by 63% between September 2020 and Might 2021. The same report from Avast in the UK recorded a shocking 93% improve in the usage of spyware and adware apps over an analogous interval.
If you wish to know in case your machine has been contaminated by considered one of these apps, it is best to examine your privateness dashboard and the itemizing of all apps in settings, the analysis staff says.
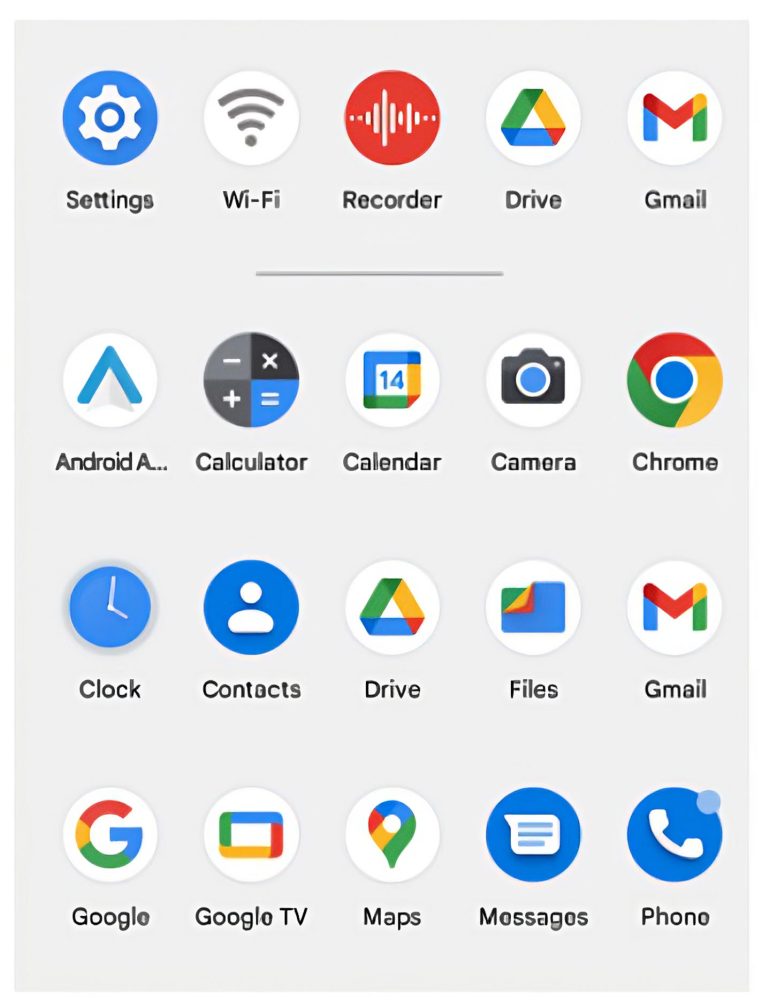
This app launcher on an Android cellphone shows app icons: the Spyhuman app put in itself because the innocuous-seeming WiFi icon. What are spyware and adware apps? Spy ware apps surreptitiously run on a tool, most frequently with out the machine proprietor’s consciousness. They gather a variety of delicate info akin to location, texts, and calls, in addition to audio and video. Some apps may even stream stay audio and video. All this info is delivered to an abuser by way of a web based spyware and adware portal. Credit score: Jacobs College of Engineering/College of California San Diego
“It is a real-life downside and we need to elevate consciousness for everybody, from victims to the analysis group,” stated Enze Alex Liu, the primary writer of the paper No Privateness Amongst Spies: Assessing the Performance and Insecurity of Client Android Spy ware Apps and a pc science Ph.D. pupil on the University of California San Diego.
Liu and the analysis staff will current their work on the Privateness Enhancing Applied sciences Symposium in the summertime of 2023 in Zurich, Switzerland.
Researchers carried out an in-depth technical evaluation of 14 main spyware and adware apps for Android telephones. Whereas Google doesn’t allow the sale of such apps on its Google Play app retailer, Android telephones generally permit such invasive apps to be downloaded individually by way of the Net. The iPhone, as compared, doesn’t permit such “aspect loading” and thus shopper spyware and adware apps on this platform are usually much more restricted and fewer invasive in capabilities.
What are spyware and adware apps?
Spy ware apps surreptitiously run on a tool, most frequently with out the machine proprietor’s consciousness. They gather a variety of delicate info akin to location, texts, and calls, in addition to audio and video. Some apps may even stream stay audio and video. All this info is delivered to an abuser by way of a web based spyware and adware portal.
Spy ware apps are marketed on to most people and are comparatively low cost–usually between $30 and $100 per 30 days. They’re straightforward to put in on a smartphone and require no specialised data to deploy or function. However customers have to have non permanent bodily entry to their goal’s machine and the flexibility to put in apps that aren’t within the pre-approved app shops.
How do spyware and adware apps collect knowledge?
Researchers discovered that spyware and adware apps use a variety of methods to surreptitiously report knowledge. For instance, one app makes use of an invisible browser that may stream stay video from the machine’s digicam to a spyware and adware server. Apps are also in a position to report cellphone calls by way of the machine’s microphone, typically activating the speaker perform in hopes of capturing what interlocutors are saying as effectively.
A number of apps additionally exploit accessibility options on smartphones, designed to learn what seems on the display screen for vision-impaired customers. On Android, these options successfully permit spyware and adware to report keystrokes, for instance.
Researchers additionally discovered a number of strategies the apps use to cover on the goal’s machine.
For instance, apps can specify that they don’t seem within the launch bar after they initially open. App icons additionally masquerade as “Wi-Fi” or “Web Service.”
4 of the spyware and adware apps settle for instructions by way of SMS messages. Two of the apps the researchers analyzed didn’t examine whether or not the textual content message got here from their consumer and executed the instructions anyway. One app might even execute a command that would remotely wipe the sufferer’s cellphone.
Gaps in knowledge safety
Researchers additionally investigated how critically spyware and adware apps protected the delicate person knowledge they collected. The brief reply is: not very critically. A number of spyware and adware apps use unencrypted communication channels to transmit the info they gather, akin to pictures, texts, and site. Solely 4 out of the 14 the researchers studied did this. That knowledge additionally contains the login credentials of the one who purchased the app. All this info could possibly be simply harvested by another person over WiFi.
In a majority of the functions the researchers analyzed, the identical knowledge is saved in public URLs accessible to anybody with the hyperlink. As well as, in some instances, person knowledge is saved in predictable URLs that make it doable to entry knowledge throughout a number of accounts by merely switching out just a few characters within the URLs. In a single occasion, the researchers recognized an authentication weak point in a single main spyware and adware service that will permit all the info for each account to be accessed by any get together.
Furthermore, many of those apps retain delicate knowledge and not using a buyer contract or after a buyer has stopped utilizing them. 4 out of the 14 apps studied don’t delete knowledge from the spyware and adware servers even when the person deleted their account or the app’s license expired. One app captures knowledge from the sufferer throughout a free trial interval, however solely makes it obtainable to the abuser after they paid for a subscription. And if the abuser doesn’t get a subscription, the app retains the info anyway.
The way to counter spyware and adware
“Our suggestion is that Android ought to implement stricter necessities on what apps can cover icons,” researchers write. “Most apps that run on Android telephones must be required to have an icon that would seem within the launch bar.”
Researchers additionally discovered that many spyware and adware apps resisted makes an attempt to uninstall them. Some additionally robotically restarted themselves after being stopped by the Android system or after machine reboots. “We suggest including a dashboard for monitoring apps that may robotically begin themselves,” the researchers write.
To counter spyware and adware, Android units use varied strategies, together with a visual indicator to the person that may’t be dismissed whereas an app is utilizing the microphone or digicam. However these strategies can fail for varied causes. For instance, official makes use of of the machine may also set off the indicator for the microphone or digicam.
“As an alternative, we suggest that every one actions to entry delicate knowledge be added to the privateness dashboard and that customers must be periodically notified of the existence of apps with an extreme variety of permissions,” the researchers write.
Disclosures, safeguards, and subsequent steps
Researchers disclosed all their findings to all of the affected app distributors. Nobody replied to the disclosures by the paper’s publication date.
With a purpose to keep away from abuse of the code they developed, the researchers will solely make their work obtainable upon request to customers that may exhibit they’ve a official use for it.
Future work will proceed at New York College, within the group of affiliate professor Damon McCoy, who’s a UC San Diego Ph.D. alumnus. Many spyware and adware apps appear to be developed in China and Brazil, so additional examine of the provision chain that permits them to be put in outdoors of those international locations is required.
“All of those challenges spotlight the necessity for a extra artistic, various, and complete set of interventions from trade, authorities, and the analysis group,” the researchers write. “Whereas technical defenses will be a part of the answer, the issue scope is far greater. A broader vary of measures must be thought-about, together with cost interventions from firms akin to Visa and Paypal, common crackdowns from the federal government, and additional legislation enforcement motion may additionally be crucial to stop surveillance from changing into a shopper commodity.”
Reference: “No Privateness Amongst Spies: Assessing the Performance and Insecurity of Client Android Spy ware Apps” by Enze Liu, Sumanth Rao, Sam Havron, Grant Ho, Stefan Savage, Geoffrey M. Voelker and Damon McCoy, 2023, Proceedings on Privateness Enhancing Applied sciences Symposium.





